The channel and Trusted Advisor industry has been hit with an ongoing phishing attack. We want to make sure you:
- Are aware of the attack
- Understand how to prevent getting infected
- Have information from experts on what to do if you get infected
- Understand how to help your customers if they ever get infected by this or any other security attack
To learn more, please join us July 24th for a special Spotlight Briefing on the Channel Phishing Attack. REGISTER NOW!
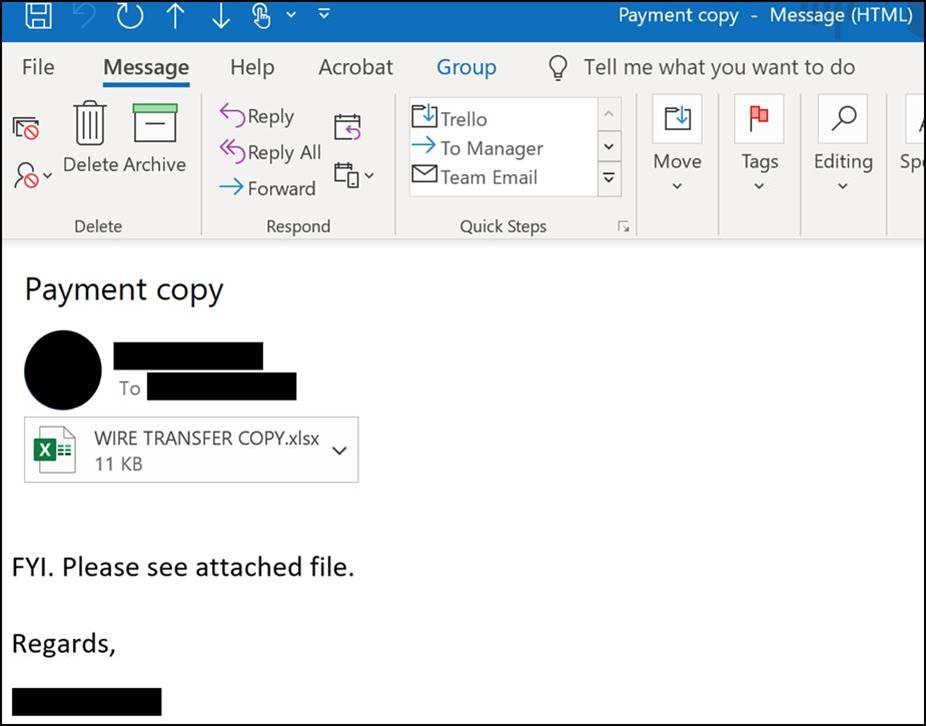
The attack that is spreading through the channel, infects the target via an innocent-looking email attachment. The email comes from someone you know that has been infected, with the correct email and signature block. It’s actually sent directly from their desktop mail application using the infected computer’s contacts.
Fig. 1 EXAMPLE of the Channel Phishing Attach Email
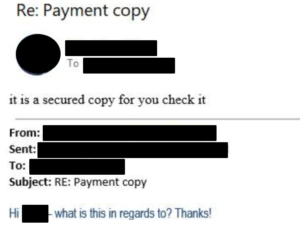
The unsuspecting user opens an attached document labeled “WIRE TRANSFER COPY.xlsx” file which contains a link. If the user then clicks on the link, and a “rootkit” virus then infects their system providing full remote control of their PC, giving the bad actor full access to the machine to launch further attacks. In this particular attack, the bad actor appears to start first by trying to infect other PC’s by going through the infected PC’s contacts and send a phishing email to the person’s community with the same attached file. If a suspecting target questions the email and attachment, the bad actor can even respond with a follow-up email to continue the charade and encourage the target to open the attachment.
Fig. 2 Follow up email from a bad actor in response to the suspicious recipient.
According to Adam Burke, from Quest Technology Management®, a security MSSP in the AVANT vendor portfolio, “The intent of the payload depends and is unknown right now. Sometimes it is looking for contacts, or specific roles within an organization. For example, the CEO or CFO, if it can access identify and spread to that account the probability of spreading further from a “credible” user is much greater. Sometimes there are multiple stages. While it’s creating the spamming effect, and everyone is trying to lock down exchange it drops a packet on an endpoint and establishes a connection/ call home. Everyone thinks it was a spamming attack and while that immediate and obvious threat was being addressed a back door was established and the automated portion is over, now the bad actors start looking around for usable data and additional opportunities.”
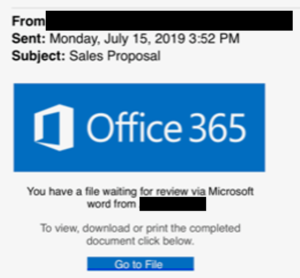
We urge the channel community to be cautious and vigilant when receiving emails with attachments, even from people you know. The pattern of this attack may change and may take other email forms. For example, the following email also is spreading through the channel community with a malicious link. It too was sent from the user’s email account and looks very legitimate:
Fig 3: Another Phishing email spreading through the channel
Here are the recommended steps from our experts if you identify an infected machine:
- Remove the machine from the network
- From another machine that is not infected login and change passwords
- Contact mail hosting company and have them assist you with remediation and blocking inbound and outbound emails
- Have the infected machine cleaned or wiped
- Be cautious of any cloud files (i.e. Dropbox, etc.) or systems that the infected machine had access to and that could have been infected by the bad actor with additional viruses. An expert may be needed to assist you with this analysis.
Here are some companies you can reach out to if you get infected.
Quest Technology Management’s Incident Response Team can be reached at:
[email protected] or 800-443-5605
- Trustwave
- Masergy
- Verizon
- Flexential
- Rapidscale
Reach out to your channel manager for contact info, or if you are an AVANT channel partner, you can find additional options to choose form in the security section of the AVANT PATHFINDER
The cyber security threats and attack have never been higher. It’s very easy for a malicious actor to launch an attack using tools readily available on the web. Unfortunately, it’s not a matter of if you will be attacked, but often a matter of when. Think about security in layers:
- PREVENT: What do I need to do to increase my chances of preventing an attack? From employee training to technology solutions.
- MITIGATE: How do I minimize the impact of an attack if and when it occurs, with backups and redundancies?
- RESPOND: Who can I call upon if I have a major incident and need experts to help respond to the attack? Be prepared today, and don’t wait till it happens.
- EVOLVE: How do I continuously stay aware and evolve my security posture as new industry threats evolve? Who is an expert that can help continuously advise me? How do I stay up to date?
AVANT has a full portfolio of security providers that can assist customers in need of assistance. You should make sure your customers understand you can help them assess their current security posture, improve their security posture, and respond when an incident occurs. If you instill one thing in your customers, it should be this:
YOU should be the 1st phone call they make in the event of a security incident!
Through AVANT, you have access to the best security MSSPs in the industry.
Stay cyber safe and let’s use this lesson as a wakeup call to enhance the security posture of our customers!